What is Cloud Infrastructure Entitlements Management?
Maximise the efficiency and cost savings of your cloud infrastructure with effective entitlements management. Our blog covers the latest strategies and best practices for managing entitlements in the cloud.
What is Cloud Infrastructure Entitlements Management?
Sometimes known as Cloud Permissions Management Solutions or Cloud Entitlements Management Solutions, Cloud Infrastructure Entitlements Management (CIEM) is the process of controlling and regulating access to cloud-based systems and services.
CIEM is a relatively new concept in the security technology industry but with changing cloud trends, it has gained prominence of late through Gartner’s 2020 report, Hype Cycle for Cloud Security.
Specialised identity-centric SaaS solutions focused on managing cloud access risk via administration-time controls for managing entitlements and data governance in hybrid and multicloud IaaS architectures.Gartner, 2020
CIEM typically involves establishing user roles and permissions for different levels of system access, providing user authentication and authorization, monitoring user activity and ensuring that the system remains secure.
This process is critical for cloud security, as it helps to ensure that only those users with the necessary permissions can access the sensitive data stored in the cloud. It seeks to identify the risks that may occur from system privileges being broader than they should be and avoiding them.
The importance of effective Cloud Infrastructure Entitlements Management
Cloud Infrastructure Entitlements Management is essential for organisations of all sizes that use cloud services providers. Supply chains and security vulnerabilities are being increasingly exploited in cyber attacks and they can pose very real threats to companies and their cloud infrastructure as more and more organisations migrate their operations over to the cloud.
CIEM helps organisations ensure that users have the appropriate access to their cloud resources and that the data and applications stored in the cloud remain secure and compliant. Entitlements management also helps organisations maintain control over their cloud infrastructure, ensuring that only authorised users can access the resources they need. Additionally, effective entitlements management can reduce costs associated with cloud services and help organisations adhere to industry best practices.
Gartner analysts predict that by 2025, more that 85% of companies worldwide will have adopted a ‘cloud-first’ strategy, and that these will not be able to be effectively implemented and maintained without good and reliable security measures, such as CIEM. Therefore, it’s more important now than ever before to implement effective CIEM into your organisation.
The benefits of adopting an entitlements management strategy
There are many benefits to adopting CIEM into your cloud infrastructure. For example, increased cloud security, great efficiency, significant cost savings, higher performance and optimisation. In addition, CIEM is extremely useful in a multi-tenant or a multi-cloud environment as it allows for excellent visibility into entitlements.
Let’s have a look at some of the benefits in a little more detail…
Customisable solutions for your unique business needs
CIEM solutions give businesses the ability to customise their solutions to meet their specific needs and objectives. Each company has different requirements according to their operations, and having the ability to utilise CIEM to directly meet those needs is highly valuable.
Here are some customisable features that organisations can tailor to suit their business needs:
- Cloud-based CIEM – This is a great way to quickly and easily deploy a comprehensive customer identity and access management system. It provides a unified platform to manage customer identities, access control and authentication across multiple devices and applications. It is also easily customisable to meet the needs of your organisation.
- Multi-factor authentication CIEM – This feature allows for the implementation of a secure authentication process that requires multiple factors in order to gain access. This solution can be customised to include a variety of authentication methods, such as biometrics, one-time passwords and hardware tokens.
- Single sign-on CIEM – This enables users to access multiple applications and services with the same credentials. This is a convenient and secure way to manage customer identities, as well as improve customer experience.
- Identity federation CIEM – This provides a secure, consistent way to manage customer identities across multiple organisations. This solution can be customised to meet the specific requirements of each organisation.
- Identity governance CIEM – This enables organisations to define and manage access policies for their customers. This solution is customisable to meet the specific needs of each organisation, and can be used to ensure compliance with industry regulations.
Improved performance and cost savings through optimised entitlements
Improved performance and cost savings can be achieved through the optimisation of entitlements. By reviewing and analysing user access rights and privileges, organisations can identify which entitlements are necessary and which can be revoked, reduced or consolidated. This process can also help to ensure that users only have access to the resources they require and reduce the risk of unauthorised access to sensitive systems or data.
Additionally, optimisation of entitlements can lead to improved performance by reducing the amount of time spent on manual processes such as granting and managing access.
Finally, reducing the number of unnecessary entitlements can also lead to cost savings, as organisations no longer need to pay for access to resources that are not being used.
Automated solutions to optimise efficiency and cost
CIEM provides a comprehensive set of features that help companies manage their cloud infrastructure more efficiently, such as automated provisioning, resource utilisation management, automated patching and compliance reporting. In addition, CIEM provides cloud automation and orchestration capabilities that help companies reduce operational costs and improve their agility.
Secure and compliant entitlements management
In order to maintain the security of your cloud systems, it is important that your entitlements management system is secure and offers comprehensive protection from risk.
CIEM offers secure and compliant entitlements management by providing a centralised platform for managing access to all applications and services. The platform offers features for managing user identities, authentication and authorisation and user access policies.
CIEM also provides automated workflow processes for tracking and managing changes to user access rights and permissions. Additionally, CIEM provides robust audit and reporting capabilities to ensure compliance with regulatory requirements and best practices.
Real-time visibility and control over your cloud entitlements
One key aspect of maintaining a secure and compliant entitlements management system is through the use of real-time visibility and control of your cloud elements. This helps to maintain security by monitoring and enforcing user access rights and application privileges. It is achieved by aggregating cloud data from all cloud environments, enabling administrators to monitor every user’s activities and privileges on individual cloud services.
In addition, CIEM allows administrators to apply granular access control rules and automatically detect any policy violations in order to prevent unauthorised access. This helps to ensure that only authorised users have the necessary privileges to access data and applications in the cloud, while helping to protect the organisation from potential data breaches.
Real-time visibility and control over their cloud entitlements also allows businesses to keep track of their cloud usage, identify areas of potential cost savings and quickly address any security vulnerabilities. By monitoring their cloud usage, businesses can quickly identify any unauthorised access or usage and take corrective action to prevent similar incidents in the future. Additionally, businesses can use real-time visibility and control to identify opportunities to optimise their cloud environment for performance, reliability and scalability.
With these, businesses can gain visibility into their cloud usage in order to make informed decisions about how to best manage their cloud resources and optimise their costs. This helps them to ensure that their cloud environment is secure, compliant and optimised for performance.
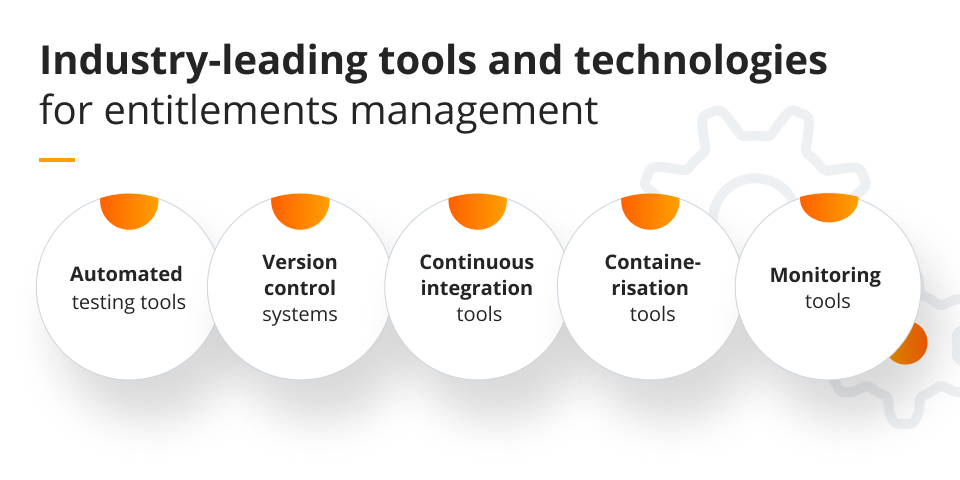
Industry-leading tools and technologies for entitlements management
There are lots of tools and technologies on the market for CIEM, with some being better and more useful than others. Here are some of our top picks of industry-leading tools and technologies for entitlements management:
- Automated testing tools: Automated testing tools such as Selenium, Appium and Ranorex are essential for CIEM in order to quickly and accurately test changes in an application.
- Version control systems: Version control systems such as Git and Subversion are critical for CIEM in order to track changes in an application and ensure that all changes are tracked and tested.
- Continuous integration tools: Continuous integration tools such as Jenkins and Travis CI are essential for CIEM in order to automate the process of building, testing and deploying applications.
- Containerisation tools: Containerisation tools such as Docker and Kubernetes are useful for CIEM in order to quickly deploy and scale applications.
- Monitoring tools: Monitoring tools such as New Relic and Datadog are invaluable for CIEM in order to monitor application performance in real-time and identify any potential issues.
Summary
Cloud Infrastructure Entitlements Management is an extremely useful asset to any modern company. There are undoubtedly countless benefits of integrating it into a cloud environment to make certain that it is secure and that users only have access to the resources they are authorised to use. Many companies are using CIEM to protect their data, prevent unauthorised access and improve overall security.
When using CIEM, it is also important to take into account the best practices for optimal usage, including defining user roles, setting access limits, monitoring user activity, and regularly reviewing access rights.
Overall, as we move into a more comprehensively digitalised world, choosing the right cloud service provider who can integrate CIEM into your business is essential.