Security in relationship with outsourced IT vendors
There is no doubt that we are witnesses to how traditional licensing models are fading into obscurity, as well as, work organisation in which all processes must be executed in-house. More and more, we are dealing with situations, where the growing number of products is sold as a service, similar to the fact, that companies are more eager to delegate works, which were not considered as outsource-ready just a couple of years ago.
The growing significance of security
Often, while researching blogs of experienced programmers who write about how software development have changed during the last two decades, we may face opinions, that twenty years ago little attention was paid to security in comparison to the current times. Essentially, it was a marginal issue, often treated without attention. It was possible due to the fact the negligence effects in security were not as harmful – truth be told we had dealt with cataclysms such as the ILOVEYOU virus, however, who thought that the most common target of attacks would not be a single user, but large organisations, from which one may demand payment, or paralyse their infrastructure for entire weeks?
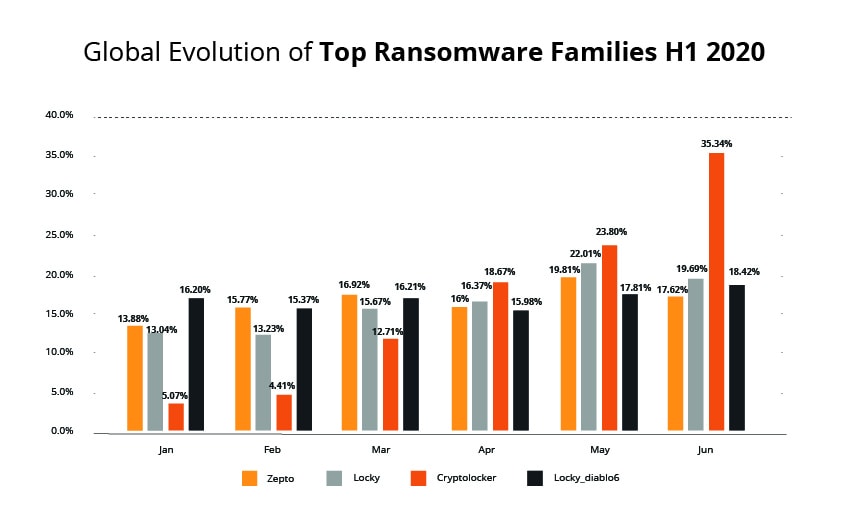
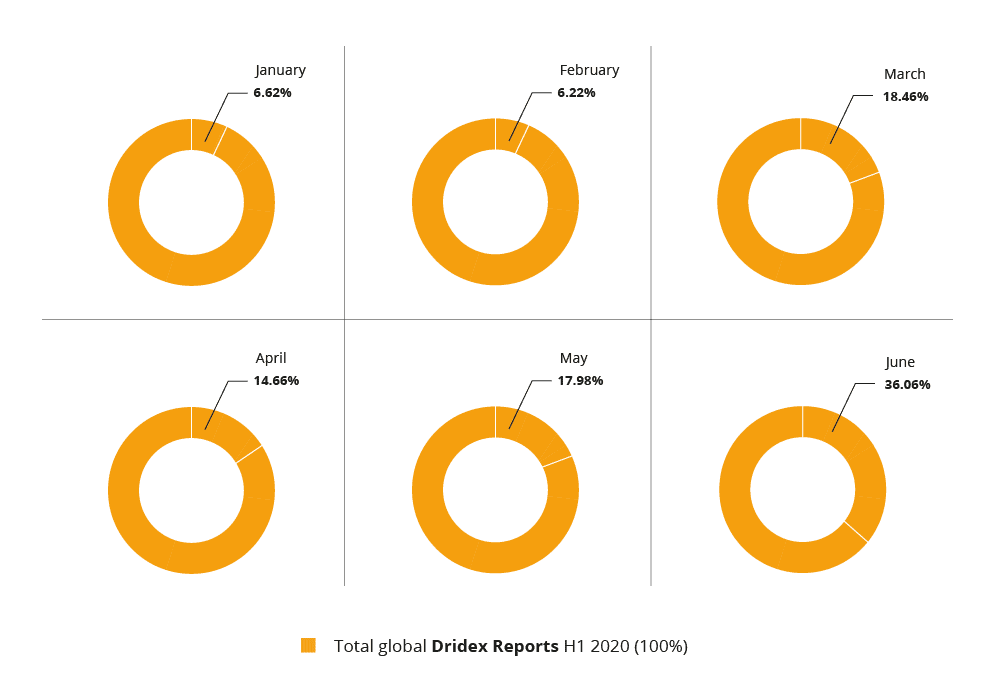
Currently, the landscape of cyberthreats looks quite different – it is constituted by large ransomware campaigns aimed against corporations, often combined into double extortion attacks, are capable of threatening organisations with enormous losses. Moreover, in the time of total internet centralisation, customers fall victim to the attacks against companies. Previously, an attack on Microsoft, would indeed, impede the functioning of a corporation, however, it would not sever the access to the basic software used at companies and in homesteads – e.g. Windows or the Office package. Currently, when both these programmes operate in the cloud infrastructure, which is nothing more than external servers of the developer, an attack on one company may essentially paralyse the entire world.
No one can allow themselves to say, that security can in any way be neglected. Quite the contrary, even small organisations, on the consumer side even, i.e. the end users, display a much larger awareness of the threats that await, similar as they display the increasing awareness of the importance of software security.
Security in software development outsourcing
All the, aforementioned overlapping phenomena, can be clearly seen using the software development outsourcing example – a complex process, translating to a truly symbiotic relation between two companies, where security should play a major role. We are speaking of a situation where we involve an external company in operations, the execution of which would be impossible without revealing vulnerable information, such as business plans or broad know-how.
Therefore, questions arise – how to secure the company infrastructure and particularly vulnerable data, while maintaining the ease of collaboration with an outsourcing partner. It would be difficult to solely rely on years of collaboration and grounded trust – it would be enough for the partner to take a new employee in, who, due to certain reasons (a job for a competing company, or frustration due to being fired) decides to sabotage operations.
In such situations vendor contracts may offer security, as they force both parties to apply universally accepted security norms and good practices. Within the European market, we may present meticulously designed procedures – e.g. based on regular external and internal audits, credentials’ limitations for work groups, or appropriately implemented policies regarding access to vulnerable resources – which may efficiently limit the risk of any data leaks. Obviously, such procedures may be successfully implemented in relations with bespoke software vendors, as they largely refer to universally applied security and access levels, or, e.g. the policy of data management.
An example of a situation, where vendor contracts defined the applied security norms insufficiently, was the 2017 Petya/NotPetya campaign. Then, even the best protected infrastructure was infected with ransomware, as one of the companies participating in the supply chain (particularly, the Ukrainian producer of software used in collaboration of local companies with institutions), did not employ sufficient norms. The company infrastructure was breached, their supply chain was hijacked, and a number of computers, difficult to estimate, were infected, as it was believed, that the update channel was secure. It would suffice to execute the application of norms within contracts between parties regularly, and the cataclysm may have been prevented.
Instead of outsourcing security – security outsourcing?
However, it is increasingly noticed that high security standards should be maintained bilaterally, as guaranteed by certain agreement entries, as well as, security audits, are supplemented by a relatively new approach. If we are currently delegating an increasing number of tasks, often taking advantage of the offer of external companies in the form of services, why should we treat security differently?
A similar model of approaching maintaining cooperation is favoured by the popularisation and high accessibility of broadly perceived cloud services. Then, e.g. in an externally hosted repository, the collaboration in terms of software development may take place on third-party company servers. Obviously, the contract with a partner must foresee this possibility as well, forcing the application of good practices in terms of access to the external infrastructure. However, securing it, e.g. against the aforementioned ransomware attacks, or an assortment of other threats, along with data leaks, devastating particularly in the GDPR era, is a task for the cloud provider, e.g. Microsoft or the Amazon corporation.
There are many ways to approach security, however none may be based solely on trust. A good contract, forcing the employment of clear and generally acknowledged security policies is definitely a good start. Not all organisations require security outsourcing in the form of employing external platforms, however, it is worth remembering, that their providers are often capable of ensuring a level of security, which is practically impossible to achieve by other companies who do not specialise in this area.
Is your software secure? See how our security audits can help your company and make sure your organisation is safe!