Table of contents
- Key takeaways on cybersecurity audit
- What is a cybersecurity audit?
- The role of cybersecurity audits in safeguarding your business
- What does a cybersecurity audit cover?
- The comprehensive process of cybersecurity auditing
- The far-reaching benefits of conducting a cybersecurity audit
- How often should you conduct a cybersecurity audit?
- Secure your future with Future Processing’s cybersecurity expertise
Key takeaways on cybersecurity audit
- Comprehensive examination: A cybersecurity audit thoroughly examines an organisation’s information systems, policies, and infrastructure to identify vulnerabilities and recommend improvements, ensuring robust protection against cyber threats.
- Wide coverage: These audits cover various aspects including network, data, endpoint, physical, system, and operational security, providing a holistic view of an organisation’s cybersecurity posture.
- Proactive risk management: Regular cybersecurity audits help proactively identify and mitigate risks, ensuring compliance with industry regulations, improving incident response capabilities, and enhancing overall data protection.
What is a cybersecurity audit?
Let’s start by explaining what a cybersecurity audit is.

A cybersecurity audit is a comprehensive examination of an organisation’s information systems, policies, procedures and infrastructure to assess and ensure the effectiveness of its cybersecurity measures.
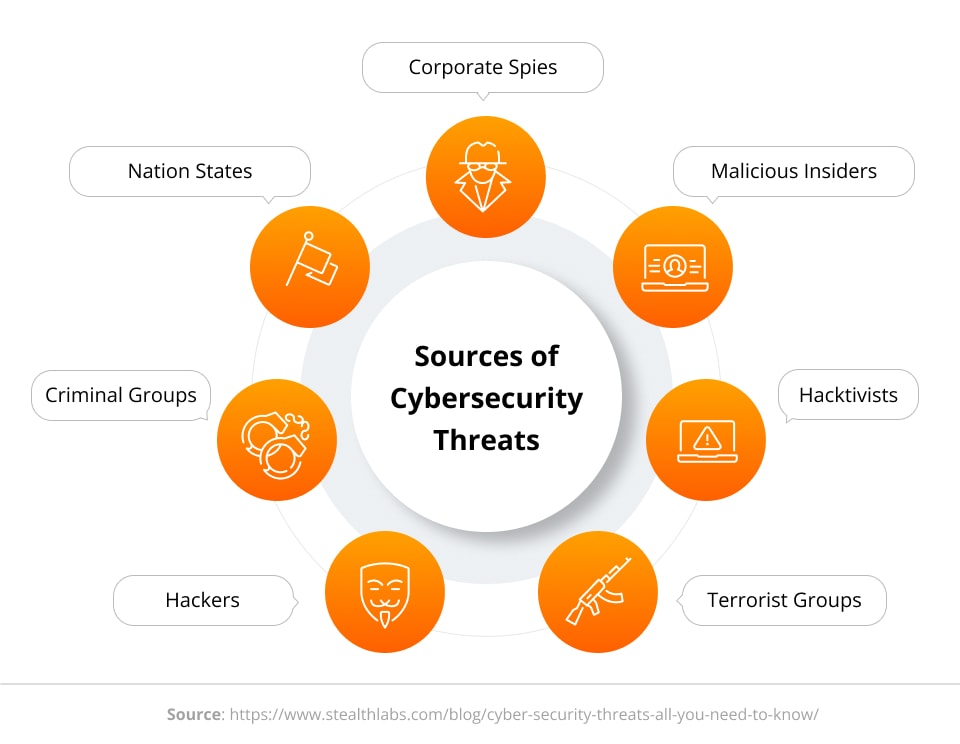
If you decide to conduct a cybersecurity audit, people doing it for you will try to find as many vulnerabilities in your systems as possible to identify different cyber threats and ways cybercriminals may hack your assets.
There are many different types of cybersecurity audits, but they all have a common goal – to identify vulnerabilities, weaknesses, and potential threats to the organisation’s information assets, and to recommend improvements and safeguards to mitigate those risks.
Simply put, cybersecurity audits allow you to stay safe and avoid cyberattacks. If you conduct them regularly, you can rest easy!
The role of cybersecurity audits in safeguarding your business
All cybersecurity audits play a pivotal role in safeguarding your business and its assets, as they provide a comprehensive evaluation of security measures you are using.
They allow for proactive identification of security vulnerabilities in your systems, for enhanced protection of sensitive data, compliance assurance that reduces the risk of legal and financial repercussions, identification of security risks and improvement of security processes and systems.
Such security controls are indispensable if you want your business to be save and your data to be protected. Statistics say that a cyberattack occurs roughly once every 39 seconds, while malware attacks cost companies an average of $2.6 million. Those two numbers are more than enough to convince everyone how important cybersecurity solutions really are!
Want to know more about cybersecurity that can help you secure your business? Check out these:
- How to develop a cybersecurity strategy in 6 steps?
- What is cyber resilience and what are the benefits?
- Security architecture 101: understanding the basics
- How to create a cyber incident response plan?
What does a cybersecurity audit cover?
A cybersecurity audit covers a wide range of areas within an organisation.
The specific components of a cybersecurity audit may vary based on the organisation’s size, industry, and the nature of its information systems, but there are some common elements typically covered in every cybersecurity assessment.
They include:
- network security, meaning examination of firewalls, network controls, antivirus configurations and network monitoring;
- data security, meaning examination of data encryption practices;
- endpoint security, meaning evaluation of antivirus and anti-malware solutions on endpoints;
- physical security, meaning evaluation of physical security measures to protect data centres and critical infrastructure;
- system security, meaning evaluation of access controls;
- operational security, covering security processes and policies.

The comprehensive process of cybersecurity auditing
While it’s really difficult to provide you with a detailed list of things to do as a part of a thorough cybersecurity audit as each of them is slightly different and depends both on the organisation and on the team performing it.

Did you know that 43% of organizations have lost existing customers due to cyber attacks? (source: “Hiscox Cyber Readiness Report 2024”)
Identify potential risks and vulnerabilities in your systems to protect your organisation from all angles! Talk to our experts about a cybersecurity audit tailored to your needs.
To help you get ready for it we prepared a step-by-step overview of a typical cyber security audit process:
- Clearly define objectives and scope. Identify relevant compliance standards and regulatory requirements;
- Get ready by gathering information about the organisation’s infrastructure, network architecture, and critical systems, and by reviewing existing cybersecurity related policies, procedures and documentation;
- Conduct a risk assessment to identify potential cyber risk, threats and vulnerabilities;
- Develop a detailed audit plan, including timelines and resource allocation;
- Conduct a thorough vulnerability assessment and penetration testing on network infrastructure and critical systems; evaluate user access permissions, authentication mechanisms, and privilege levels;
- Analyse policies, procedures and controls and verify whether they align with industry best practices and compliance requirements;
- Conduct data protection assessment, physical security inspection, and incident response testing;
- Think of areas such as third party risks, mobile and wireless security assessment, cloud security and security architecture analysis;
- Develop a remediation plan for addressing identified vulnerabilities and weaknesses;
- Follow-up, think of continuous improvement and offer employees training to enhance their awareness and skills in cybersecurity best practices.
The far-reaching benefits of conducting a cybersecurity audit
Cybersecurity audits provide far-reaching benefits to all organisations, no matter their size or industry they are a part of.
There are so many of them, it’s difficult to list them all, so let’s stick to some most important ones:
- Identification of vulnerabilities in systems and networks, which reduces the risk of exploitation by cyber attackers, protects sensitive data, and prevents potential security breaches.
- Prioritisation and mitigation of risks based on their impact and likelihood, which enhances the organisation’s ability to make informed decisions about resource allocation and risk reduction strategies.
- Adherence to industry regulations and legal requirements, such as NIS 2.0, DORA, ISO27001, or Cyber Resilience Act, which reduces the risk of legal and financial consequences associated with non-compliance.
- Enhanced security policies that provide clear guidelines for employees, improve security awareness, and establish a foundation for a robust security culture.
- Improved incident response capabilities that reduce the time and impact of potential security incidents by ensuring a well-prepared and effective response.
- Enhanced data protection and privacy, allowing for safeguarding sensitive information, maintaining customer trust, and avoiding data breaches.
- Improved access controls, which reduces the risk of unauthorised access and ensures that employees have appropriate levels of access based on their roles.
- Improved employee awareness, which leads them to recognise and respond to potential security threats, reducing the human factor in cybersecurity incidents.
- Cost savings, as security issues often lead to costly incidents, which mean financial losses, reputational damage, and legal consequences associated with security breaches.
- Better customer and stakeholder trust, achieved by demonstrating a commitment to cybersecurity best practices.
How often should you conduct a cybersecurity audit?
You may be wondering how often you should conduct a cyber security audit to get all the benefits associated with it.
A good practice is having it done once a year, but remember that the frequency of cyber adulting depends on several different factors such as the size of your organisation, your resources, number of systems in place and the complexity of procedures.
There are some moments when you should conduct a cybersecurity audit no matter when was the last time you did it. Such moments include all significant operational changes, takeovers or when new compliance standards comes to live. If in doubt, speak to an experienced consultant – they will advise you on how to best act in order to stay secure.
Secure your future with Future Processing’s cybersecurity expertise
If the thought of cybersecurity auditing process gives you a headache, get in touch with us. At Future Processing we have extensive experience in identifying potential risks and vulnerabilities in our clients’ systems to protect them from all angles.
Our highly efficient cybersecurity specialists will help you uncover and fix potential threats and minimise the risk of data breaches, giving you a better protection against cybercriminals. Contact us today to secure your future!







